Every project carries uncertainty. Whether you are building infrastructure, launching software, or organizing a large-scale event, unexpected obstacles can derail timelines and budgets. Project risk management is not about predicting the future with perfect accuracy; it is about preparing for possibilities that could impact your objectives. This guide provides a structured approach to identifying, assessing, and handling risks effectively.
Risk management is a proactive discipline. It moves teams from a reactive stance, where fires are put out after they start, to a proactive stance where hazards are spotted and neutralized before they cause harm. By integrating risk practices into your workflow, you protect the value of the project and ensure smoother delivery.
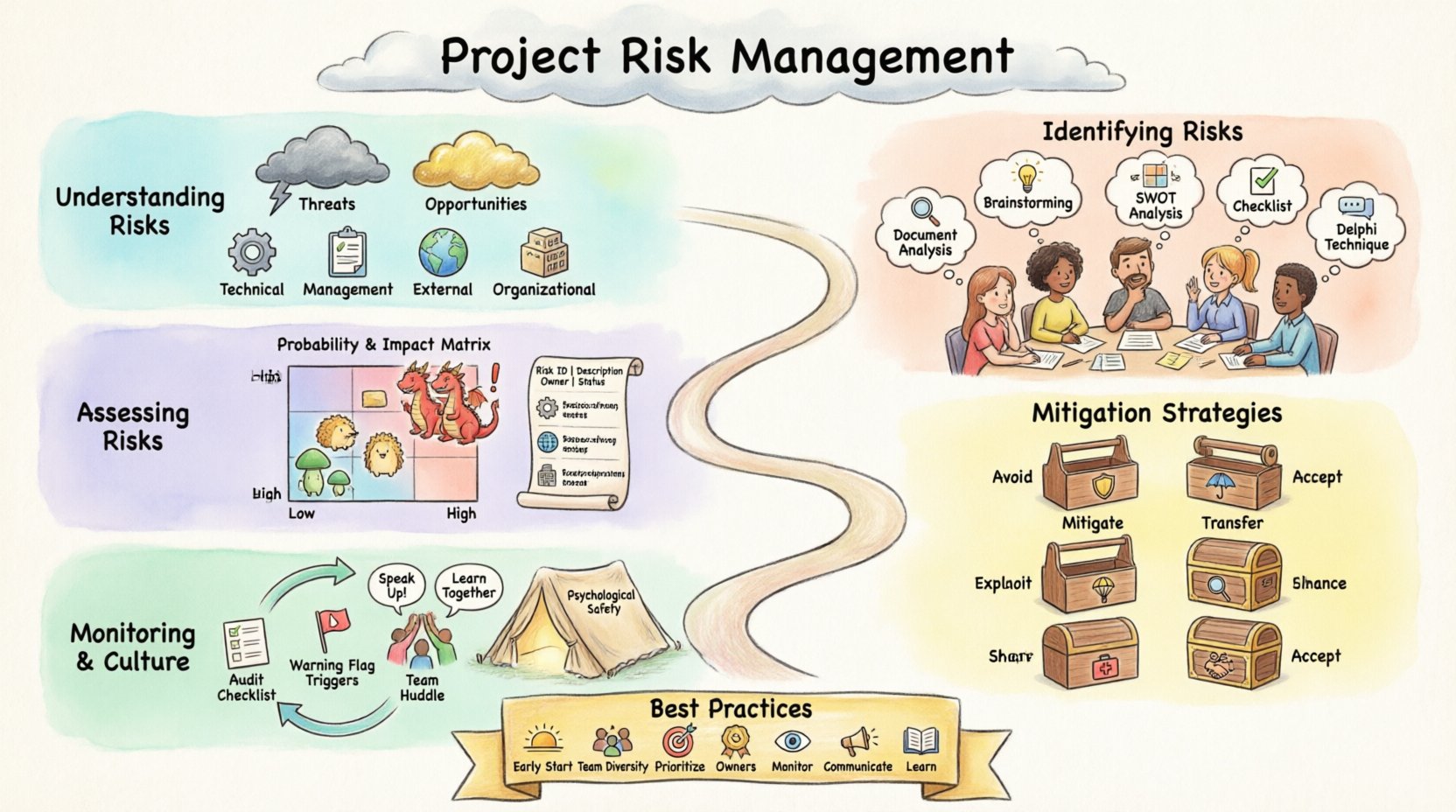
Understanding Project Risks 🧐
Before diving into methods, it is essential to define what constitutes a risk in a project context. A risk is an uncertain event or condition that, if it occurs, has a positive or negative effect on one or more project objectives. These objectives typically include scope, schedule, cost, and quality.
- Threats: Negative impacts that must be avoided or minimized.
- Opportunities: Positive impacts that can be exploited to benefit the project.
Many practitioners focus solely on threats, but opportunities are equally vital for value creation. Ignoring risks leads to surprises that consume contingency reserves and stress the team. Recognizing risk types helps in categorizing them for better handling.
Common Categories of Risk
Risks can be grouped to ensure comprehensive coverage. Typical categories include:
- Technical Risks: Issues related to technology, architecture, or performance.
- Management Risks: Poor planning, communication breakdowns, or resource allocation errors.
- External Risks: Market shifts, regulatory changes, or supplier failures.
- Organizational Risks: Internal politics, budget cuts, or shifting priorities.
Understanding these categories ensures that the team looks beyond the obvious technical hurdles and considers the broader ecosystem in which the project operates.
Identifying Potential Risks 🔍
Identification is the foundation of risk management. If a risk is not recorded, it cannot be managed. This phase involves gathering information from various sources to uncover potential issues. It is an iterative process that should continue throughout the project lifecycle.
Techniques for Identification
There are several proven methods to generate a list of risks. Relying on a single source is rarely sufficient. A combination of techniques yields the most robust risk register.
- Document Analysis: Reviewing project plans, assumptions, and constraints. Often, risks are hidden in the fine print of requirements or assumptions that have not been validated.
- Brainstorming Sessions: Group discussions with the team and stakeholders. This leverages collective experience. Ensure a safe environment where participants feel comfortable sharing concerns without fear of blame.
- SWOT Analysis: Assessing Strengths, Weaknesses, Opportunities, and Threats. This helps contextualize risks within the broader organizational strategy.
- Checklist Analysis: Using historical data from similar past projects. This is efficient for common risks that recur across industries.
- Delphi Technique: A structured communication method where experts provide anonymous feedback. This reduces the influence of dominant personalities and encourages honest input.
- Root Cause Analysis: Asking “why” repeatedly to find the underlying cause of a known problem. This helps identify risks that stem from systemic issues.
Who Should Participate?
Risk identification is not just the responsibility of the project manager. It requires diverse perspectives:
- Project Team: They know the technical details and daily hurdles.
- Subject Matter Experts: They provide insight into specific domains like legal, security, or engineering.
- Stakeholders: They understand the business impact and external dependencies.
- Sponsors: They can highlight strategic shifts or budget constraints.
Inviting these groups ensures that blind spots are minimized. For example, a developer might see a technical debt risk, while a stakeholder might see a market timing risk. Both must be captured.
Assessing and Prioritizing Risks 📊
Once risks are identified, they must be evaluated. You cannot mitigate everything at once. Resources are finite, so you need to prioritize based on the potential severity and likelihood of occurrence. This process is known as risk assessment.
Qualitative vs. Quantitative Analysis
Qualitative Analysis is subjective and relies on experience. It uses scales like High, Medium, Low to rank risks. It is fast and useful for initial filtering.
Quantitative Analysis is numerical. It uses data to estimate the probability and financial impact. This is more rigorous but requires more data and time. It is often reserved for high-priority risks.
The Probability and Impact Matrix
A common tool for prioritization is the Probability and Impact Matrix. This grid plots risks based on two axes:
- Probability: How likely is the event to happen? (e.g., 0% to 100%)
- Impact: How severe would the consequence be? (e.g., Cost overrun, schedule delay, safety issue)
By combining these two factors, you calculate a Risk Score. High-probability and high-impact risks fall into the “Critical” zone and require immediate attention. Low-probability and low-impact risks may only need monitoring.
Example Risk Register Structure
To manage this data effectively, a Risk Register is maintained. It serves as the central repository for all risk information.
| Risk ID | Description | Probability | Impact | Score | Owner |
|---|---|---|---|---|---|
| R001 | Key staff member leaves | Medium | High | 8 | HR Manager |
| R002 | Vendor delivery delay | High | Medium | 6 | Procurement Lead |
| R003 | Requirement change | High | High | 9 | Project Manager |
This table provides a snapshot of the risk landscape. The Score helps in quick sorting. The Owner ensures accountability.
Developing Mitigation Strategies 🛠️
Once risks are prioritized, you need a plan. This is the risk response planning phase. The goal is to alter the risk profile to a more acceptable level. There are four primary strategies for threats and two for opportunities.
Strategies for Threats
When facing negative risks, you can choose from the following approaches:
- Avoid: Change the project plan to eliminate the risk entirely. For example, removing a feature that relies on unproven technology.
- Mitigate: Reduce the probability or impact. For instance, implementing additional testing phases to lower the chance of defects.
- Transfer: Shift the risk to a third party. Insurance or outsourcing are common examples.
- Accept: Acknowledge the risk and prepare a contingency plan. This is for risks that are too costly to avoid or mitigate.
Strategies for Opportunities
Positive risks require different handling to ensure they are realized:
- Exploit: Ensure the opportunity definitely happens. Assign top resources to a task to finish early.
- Enhance: Increase the probability or impact. Add features that might speed up adoption.
- Share: Partner with others to capture the opportunity. Joint ventures are a form of sharing.
- Accept: Be willing to take the benefit if it occurs, but do not actively pursue it.
| Strategy | Description | Example Action |
|---|---|---|
| Avoid | Eliminate the threat | Drop a high-risk technology |
| Mitigate | Reduce likelihood or impact | Conduct prototype testing |
| Transfer | Shift responsibility | Buy insurance policy |
| Accept | No proactive action | Allocate contingency budget |
Each risk response must have a clear owner and a timeline. A strategy without an owner is likely to be ignored. Furthermore, responses should be cost-effective. Spending more to mitigate a risk than the risk is worth is poor management.
Monitoring and Controlling Risks 🔄
Risk management does not end with planning. Risks evolve. New risks emerge, and old ones may change in probability or impact. Continuous monitoring is required to keep the risk profile accurate.
Risk Audits
A risk audit is a structured review of the risk management process. It examines:
- Are the risk responses effective?
- Are the owners fulfilling their responsibilities?
- Is the risk register up to date?
Audits help improve the process for future projects. They identify gaps in the current approach and suggest corrective actions.
Trigger Indicators
Not all risks happen suddenly. Many come with warning signs. These are called trigger indicators. Identifying them allows for early action. For example, if a supplier is known to be late, a trigger might be a missed status report three days before the deadline. This signals that the risk is imminent.
Residual and Secondary Risks
Residual Risks are what remain after a response has been implemented. You must always account for these. Even after mitigation, some risk usually persists.
Secondary Risks are new risks created directly by implementing a response. For example, transferring a task to a vendor might mitigate cost risk but introduce a quality risk. These must be tracked as well.
Fostering a Risk-Aware Culture 🤝
Tools and registers are useless if the team is afraid to report issues. A healthy project culture encourages transparency. When team members feel safe raising concerns, risks are caught earlier.
Psychological Safety
Leaders must model vulnerability. Admitting uncertainty invites collaboration. If a leader pretends to know everything, the team will hide problems until it is too late. Create forums where bad news is welcomed because it allows for early intervention.
Communication Plans
Risk communication should be regular. Instead of burying risk data in a monthly report, discuss it in stand-ups or steering committee meetings. Keep stakeholders informed about the status of critical risks. Transparency builds trust.
Lessons Learned
At the end of a project, review the risk register. Compare planned risks with actual occurrences. What was missed? Why? Documenting these lessons ensures that the organization learns and improves its risk identification process for the next initiative.
Training and Development
Risk management skills should be part of the team’s development plan. Not every member needs to be an expert, but everyone should understand the basics. This creates a shared language for discussing uncertainty and ensures that risk thinking is embedded in daily work.
Summary of Best Practices
To conclude this guide, here are the core principles to remember for effective project risk management:
- Start Early: Begin identification during the planning phase.
- Involve Everyone: Leverage diverse perspectives for better coverage.
- Prioritize Ruthlessly: Focus resources on high-probability, high-impact risks.
- Assign Owners: Every risk needs a person responsible for monitoring it.
- Monitor Continuously: Update the register as the project progresses.
- Communicate Openly: Ensure stakeholders understand the risk landscape.
- Learn from History: Use past project data to inform current assessments.
Implementing these practices does not guarantee success, but it significantly increases the odds. Projects are complex systems. By managing the uncertainties within them, you create a stable environment where the team can focus on execution rather than reacting to crises. This discipline separates successful deliveries from those that struggle to reach the finish line.
